A faithful HackMii reader (zeldarock) spent some time with AnyTitle Deleter and tried to clean everything odd off his Wii, and used the HackMii Installer to uninstall the HBC and BootMii/boot2. He then sent his Wii into Nintendo (of America) to try to get them to repair a noisy drive; the warranty had expired, and he just wanted to pay them to repair the drive.
After they received the Wii, they wrote him back and said that because he had unauthorized software installed (something they could not fix themselves — but more on this later), it would cost $200 for them to do any repair. He had them just send him back the Wii, they would not work on it. They sent him back his Wii, and then he reinstalled BootMii/boot2 and dumped the NAND and sent it to us to figure out what he had missed and anything else we could gain from the image.
I have a few theories as to what they detected, based on what things he did not manage to delete — and for a while, that’s all we had to go on, and it wasn’t going to make for a very interesting article. However, several hours with 0xED and grep and xxd paid off, and I found some traces of the disc they ran to detect “Illegal software”. Unfortunately, I was only able to find part of the data section of the main DOL of the disc, and not the code, so I don’t have actual screenshots to share — you’ll have to use your imagination this time. (If anyone has sent a Wii in to Nintendo for repair in the past few months, and received the same Wii back — no refurbs! — I’d love to see a NAND dump, especially if you took one right after you received it back. I may be able to reconstruct the rest of the disc.)
Here is the raw output of ‘strings’ on the relevant part of the data section:
*******************************************************
Check Disk for Pre-Repair Process
Disc TitleId : 0x%08x(Hi) 0x%08x(Lo)
Num of Checking : %d
This running is "First Running".
Start Region Address : 0x%08x
End Region Address : 0x%08x
main.cpp
*** EndSaveRegionAddr has been over rang ***
This running is "Restarted running".
Using language is Japanese.
Using language is English.
NRChecker is not inserted at SI port %d.
Waiting ejecting disk.
InitSD is failed.
Error. Line=%d
Start Checking Process.
Restart Disc...
Reset...
Shutdown...
End of Application
Unknown
Item %d : Load data from 0x%08x
Item %d : Save data to 0x%08x
Deleting the save data of SetPersonalData.wad...
Deleting the save data of DigicamPrintChannel...
/title/%08x/%08x/data/nocopy
NANDPrivateDelete : delete %s : %d
/title/%08x/%08x/data
/title/%08x/%08x/data/banner.bin
Searching unauthorized rewritten savedata...
/title/%08x/%08x/data/%s
zeldaTp.dat
/title/%08x/%08x/data
Checking %s
NANDOpen : %s(%d)
CheckSavedataZD : return false. This save data is unauthorized rewittern data.
Searching unauthorized title...
Unauthorized title num with checking ticket: %d
Unauthorized title num with checking TMD: %d
*** SearchUnauthCh_CheckTickets ***
Found ticket file num is %d
Result code of checking 0x%016llx is %d
*** SearchUnauthCh_CheckTMDs ***
Number of Home Directory is %d,
[%03d]Getting information about title id "0x%016llx"
- Title Name : %s
- TitleID : 0x%016llx
- Type : %d
- Visible : %d
- Status : %d
AnalyzeTitle : OSGetTitleStatus failed(%d).
/title/%08x/%08x/content/%08x.app
Pre-repair Check Disk ver%s
Pre-repair Check Disk ver%s - Detail
Pre-repair Check Disk ver%s - Delete
Pre-repair Check Disk ver%s - Launch Mode
Pre-repair Check Disk ver%s - Output File
------------------------------------------
----------------------------------------------
Serial Number: %s
Waiting to Start
Processing
Complete
%d.??? >%s
%d.Altered Save Data Detection >%s
%d.Illegal Channel(s) Detection >%s
%d.Use of Copy Disk Detection >%s
Checking the following item(s)...(%d/%d)
Check is complete.
Press A Button to display detail screen.
Delete All Altered Save Data and Illegal Channel(s)/Firmware?
Detected %d pieces of data
No Data
Detected illegal channel(s) >
Press A Button to restart.
Automatic restart begins after %d seconds.
%2d/%2d [Title ID/Name]
%s%2d 0x%016llx(%s)
"%s"
[Type] [Visible] [Status]
%s %s %s %s
Detected %d title(s)
Press Button B to return to previous screen.
Deleting data...
Altered Save Data Deletion >%s
Illegal Channel/Firmware Deletion >%s
If you want to launch Wii illegal channel,
Select the channel and push A button.
Launch the following title?
Title ID: 0x%016llx(%s)
Title Name: "%s"
ID: 0x%016llx(%s)
Push DOWN Button to display next page.
<>
<>
<>
<>
Serial Number
Device Id
Wii Menu
Wireless MAC
Bluetooth MAC
BT MAC
WC24 Count
WC24 Stage
WC24
Shopping
Not Used
(No File)
(Initial)
(Generated)
(Registered)
(Unknown)
%d. %s
(DiscNum. %d GameVer. %d)
%d. %s
(DiscNum. %d GameVer. %d)
%d. TitleName: %s
DiscNum: %d GameVer: %d
Error: 0x%08x(%d)
DateTime: 0x%08x(%d)
Status: 0x%08x(%d)
Control: 0x%08x(%d)
NextOffset: 0x%08x(%d)
%d. TitleName:%s
DiscNum:%d GameVer:%d
Error:0x%08x(%d)
DateTime:0x%08x(%d)
Status:0x%08x(%d)
Control:0x%08x(%d)
NextOffset:0x%08x(%d)
%d DVD error record(s) has been logged.
Output the DVD error logs to SD card?
Output the meta-data of illegal channel(s)?
Insert SD card.
[%s] %s
(Deleted)
UNKNOWN
INSTALLED
NOEXISTS
DELETED
SAVEONLY
NORIGHTS
PARTIAL
FATAL
File does not exist.
File was deleted.
Error occurred during processing(%d:%d)
There is no problem with this console.
Problematic save data was detected.
Illegal channel(s)/firmware was detected.
Disc needs to be restarted.
Deleted all.
Use of copy disk was detected.
Finished to output the file.
Controller
[Main View]
UP: Back page
DOWN: Next page
A: Show the details
Controller
[Common]
LEFT: Back
RIGHT: Next
B: Back to main view
[Illegal Channels Detection]
UP/DOWN: Scroll list
1+2(GC:X+Y): Launch channel
A+2(GC:L+R): Delete illegal channels
[Use of Copy Disk]
UP/DOWN: Scroll list
1+2(GC:X+Y): Output DVD error log
[DVD Error Log]
UP/DOWN: Scroll list
1+2(GC:X+Y): Output DVD error log
InitChangeUid : NANDInit Error(%d)
InitChangeUid : ES_InitLib Error(%d)
InitChangeUid : ES_GetTitleId Error(%d)
Changing uid to %016llx
ChangeUid : ES_SetUid Error(%d)
ChangeUid : ISFS_CloseLib Error(%d)
ChangeUid : ISFS_OpenLib Error(%d)
/title/%08x/%08x/data
ChangeToGameSaveDir : NANDPrivateChangeDir Error(%d)
/ticket/%08x/%08x.tik
/title/%08x/%08x
/meta/%08x/%08x
Delete all files in %s.
NANDPrivateReadDir : %s(%d) num = %d
Returned DELETEFILES_ERR_OK_NOEXIST.
Returned DELETEFILES_ERR_FAILED.
memory allocate is failed.
NANDPrivateDelete : %s(%d)
Returned DELETEFILES_ERR_OK.
Running "DeleteProcess".
Start to delete unauthorized channels and save datas.
ATTENTION!! : current groupId is not 0.
ChangeUid to 0x%016llx : %d
NANDPrivateDelete : %s has been deleted.
/title/%08x/%08x/data/banner.bin
Running "LauchTitle".
Can not launch because target channel is not installed.
Can not launch because target module is not a channel application.
SaveResultFunc_SearchCopyDisc
LoadResultFunc_SearchCopyDisc
/shared2/test2/dvderror.dat
: Ver.%d(TMD)
: %02x:%02x:%02x:%02x:%02x:%02x
: %s %s %s %s
: %d %s
ES_InitLib is failed : %d
ES_GetTmdView is failed : %d
Memory Allocation is failed.
ES_GetDeviceId is failed : %d
NCDiGetWirelessMacAddress is failed : %d
/shared2/succession/shop.log
NANDPrivateGetStatus is failed : %d
/shared2/wc24/nwc24msg.cfg
NANDPrivateOpen is failed : %d
NANDRead is failed : %d
Running "FileOutput".
/shared2/test2/dvderror.dat
InitSD is failed.
%s%s/%08x
%s%s/%08x/%08x
%s%s/%08x/%08x/%s
H4A should not be cleared because of Broadway errata.
<< RVL_SDK - OS release build: Mar 5 2009 08:59:58 (0x4199_60831) >>
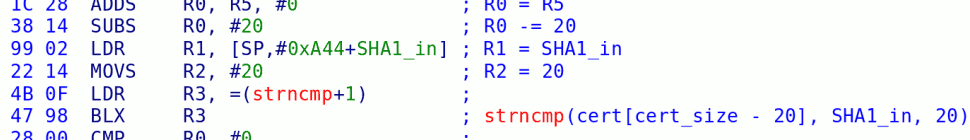
We have to do some reading between the lines here, but what we have is a disc with a fairly simple text-based UI (much like the “Wii Backup Disc” we looked at a couple of years ago) — but at least this time they’ve added colors (the BL, YE, RD tags presumably change the color of text displayed on the screen). There are a few different menus / screens you can traverse through, but the long and short of it is that they are looking for:
- Save data — they are looking to delete data from “SetPersonalData.wad” (?!) and from “DigicamPrintChannel” (which you might have if you had messed around with the regions on your Wii. They then run a check for “unauthorized rewittern data”, which seems to reuse the same old CheckSavedataZD function from the System Menu, after authenticating as RZDE/J/P.
- “Illegal Channel(s)/Firmware” — as far as I can tell, this isn’t some specific check for HBC / DVDX / whatever. This is a bit more clever — they seem to be enumerating all tickets and all TMDs on the system, and looking to see if any of them are fakesigned. This will catch pretty much anything that is, as they say, “unauthorized” that you have installed.
- “Use of Copy Disc” — I think this actually refers to their own Wii Backup Disc. It’s not entirely clear to me why they care about this. This check seems to be done by looking for the existence of /shared2/succession/shop.log. (In this context, “succession” seems to refer to the transfer of some identity info from one (presumably broken) Wii to another.)
Once they’ve done this scan, they can then do several things — most common is probably to generate a log file on an SD card. They can also launch any of the “Illegal Channels” they find, and output any of the TMD info to SD. They even have the option of deleting all of this stuff — but it seems that they’ve been told not to do this (remember, they claimed they can’t, and in fact, they didn’t before our friend got his Wii back).
In this case, what did they detect, and how? It continues to surprise me that Nintendo seems to not use any sort of special “hacked IOS” to make their lives easier — sure, the “Wii Backup Disc” came with its own (infamous) IOS16, but there wasn’t really anything special about it and we were never quite clear why they bothered. The disc runs as 1-2 and judging by its error messages, as group 0 — this means they can read and write most files in the filesystem directly, but they seem to use ES calls to do most of the work.
As for what they found — this Wii was bought second-hand, and it looks like there was a lot of “crap” on it at one point. Purely by looking for fakesigned tickets and TMDs, I found one each for 1-250 (IOS250) and 1-0 (“IOS0” — this is a bogus ticket used to gain group 0 access, Waninkoko’s old FS dumper used this and I think that AnyTitle Deleter may does as well). Something that I found that Nintendo didn’t was a bunch of crap left over from a Preloader install — extra files in 1-2’s data directory, as well as some extra files in /shared2.
28 responses so far ↓
1 11rcombs // Apr 24, 2010 at 2:41 pm
Well, that shows that AnyTitleDeleter should be deleting tickets and TMDs, as well as the titles themselves. Also, first!
2 Muzer // Apr 24, 2010 at 2:44 pm
ATD DOES delete tickets and TMDs, doesn’t it?
So yeah, presumably this was just caused by the owner of the Wii missing out IOS250 and IOS0 in his deletion spree? Nothing more?
3 DacoTaco // Apr 24, 2010 at 2:54 pm
@llrcombs : imo if you do any changes you should do it completely. hence why i let the priiloader installer/uninstaller remove all the used priiloader files on uninstall o.o
4 HyperHacker // Apr 24, 2010 at 5:50 pm
Neat. So, their disc leaves parts of its executable in flash? O.o
I suppose they’d care about their backup disc if it can be used to duplicate accounts and/or copy Wiiware titles. From the references to DVD error logs though, I think this might be looking for cases where the DVD system reported an error that can only mean you’re using a copied disc, or there isn’t a disc in the drive at all (i.e. HDD loader).
Now, what’d be really amusing is to find a buffer overflow in their disc program and take it over, to present a phony “yep, looks fine” screen… and maybe modify the system menu to dump any disc inserted. 😉
5 tech3475 // Apr 25, 2010 at 1:30 am
Knowing this, couldn’t someone write a ‘CleanMii’ app which will remove all these leftovers and possibly make the Wii as vanilla as possible again?
Also, I am surprised at Nintendos continuing use of bad code/security practices and underestimation of its users. Surely something like this could easily be run from RAM because now hackers/users know what Nintendo are looking for, allowing for better precautions before sending hacked Wiis to them.
6 bushing // Apr 25, 2010 at 3:24 am
@11rcombs: it did.
@Muzer: It was probably nothing more than missing IOS250 from his deletion spree … but I just checked, and AnyTitle Deleter adds “IOS0” and never cleans it up. I’m not even positive you *can* clean it up, since it uses that ticket/TMD to delete the files.
@HyperHacker: To improve load times, the System Menu loads the entire DOL from disc and caches it to a “cache.dat” file in 1-2’s data directory on NAND, before it even shows you the disc banner. This was probably the tail end of an erased cache file.
@tech3475: Yes and no. I don’t think that many people at Nintendo fully understand how all parts of the system fit together — for example, the people who wrote that tool may not know that the menu caches the DOL to NAND. Even if they do — the repair center did actually run another game after they ran their disc (SSBB), which deleted that data. Except, due to the nature of wear leveling, it’s extremely difficult to make sure that any specific piece of data is actually erased.
Sure, someone could make a thorough cleaning program, or at least something that runs through all of the checks that Nintendo might do. I don’t have time to start such a project, but I’d gladly play peanut gallery to anyone else who did.
7 qiantpune // Apr 25, 2010 at 5:14 am
im thinking that the UID is a great place to look to see the history of what has been run on the Wii. When deleting anything from the nand, isnt the entry left in the UID? and to get rid of it, it would involve a bit of work to ensure that all entries after the one being removed are not messed up?
8 someone // Apr 25, 2010 at 11:03 am
If you wanted to leave things so they looked like they were untouched, it strikes me that perhaps all IOSes should be checked against their checksum and the ones that fail the check should be re-installed.
Apart from one (e.g. IOS36), which should be patched with everything so the system can be manipulated and have its version number fiddled so that it’s less than the current latest version. To finalise the uninstall, Nintendo’s update could be run which should re-install IOS 36.
Another thing which can give the game away is the message board’s usage log which needs to be purified of every fake channel.
9 Wack0 // Apr 26, 2010 at 8:07 am
..but that’s simple — make the channels use nandloaders that don’t write to said usage log !!!
10 NotAWiiHacker // Apr 26, 2010 at 5:27 pm
This is intresting…..Its seems to be that the Wii keeps a “record” of everything thats been run/installed/uninstalled And from what I understand, It does this by tickets and TMDs….But what if theres something we’re (your) missing? Such as a “secret” record system? And maybe its not kept in the NAND memory…. The saves also have some way to “sign” themselves (or by other means) to make sure its a real save…. There could be something we’re (your) missing that we dont know of….
*NOTE* I use the “we’re (your)” phrase because I dont do alot of this, My ideas may not be rational or correct, because as my user states..Im not a Wii Hacker.
11 HyperHacker // Apr 27, 2010 at 7:11 am
Hm, so anyone who’s sent a Wii in for repair might have one of Nintendo’s testing/repair programs left in flash. Sounds like quite the security issue…
12 tech3475 // Apr 27, 2010 at 12:58 pm
@NotAWiiHacker, speaking purely from a point of common sense, surely they wouldn’t need to perform all these checks if there was some encrypted/obfuscated area?
@HyperHacker, this thought occured to me, however as bushing said in post 6:
“I don’t think that many people at Nintendo fully understand how all parts of the system fit together — for example, the people who wrote that tool may not know that the menu caches the DOL to NAND. Even if they do — the repair center did actually run another game after they ran their disc (SSBB), which deleted that data. Except, due to the nature of wear leveling, it’s extremely difficult to make sure that any specific piece of data is actually erased.”
13 bushing // Apr 28, 2010 at 4:41 pm
@HyperHacker: Sure, I wrote a couple of posts about other stuff we scraped from NAND, /2008/06/factory/ and /2008/07/factory2/.
Someone brought up a good point on IRC — it’s not clear how exactly they are doing this signature verification (just looking for zeroes, or is it actually running RSA on all of the tickets/TMDs)? If it’s fast enough, they might start doing this every time the system menu starts. A year ago, I’d have considered this unlikely, but —
I say this every time, but it bears repeating — do not upgrade your Wii! It feels like we’re about due for another update, and this one will probably be worse than the last.
To try to stem the inevitable flow of suggestions — there are a number of different ways to respond to a completely noxious update, but they’re all somewhat unpleasant (hard to code, invasive to the system, potential for misuse, potential for bricking the system). I even have a few of them already partially written. We’ve held back on releasing anything along those lines because there has been no need and we didn’t want to escalate the “arms race”, but if Nintendo is willing to nonchalantly update boot2 on all Wiis and put stupid checks in the system menu, we don’t have much to lose at this point.
(Meaning: We don’t need any suggestions, but we’re not willing to show all of our cards yet.)
14 Phredreeke // Apr 29, 2010 at 7:19 am
>> Someone brought up a good point on IRC — it’s not clear how exactly they are doing this signature verification (just looking for zeroes, or is it actually running RSA on all of the tickets/TMDs)?
Is there any reason why they aren’t checking ticket signatures when launching channels? Maybe they originally thought the signature check at install was impossible to bypass. xP
15 shuffle2 // Apr 29, 2010 at 9:45 am
What I find most entertaining is that even a non-technically inclined Nintendo employee could read this blog and probably discern:
1. Where (most of?) the currently exploited bugs are
2. Suggested fixes / next steps
And yet they respond with only tangentially related “bugfixes” which can brick systems – just boggles the mind.
16 leonardo2204 // Apr 29, 2010 at 11:43 pm
I’d like to know if you guys have or know some tutorial for beginners to read memory(like NOR) and how to assemble pieces like the DSi !
Thanks and you guys kick asses !
17 someone // May 1, 2010 at 7:41 am
@Wack0..
> but that’s simple — make the channels use nandloaders that don’t write to said usage log !!!
Early versions of the HBC wrote to it, as do games run through Gecko. You wouldn’t really want games from other regions to show up there.
18 tech3475 // May 1, 2010 at 12:22 pm
Couldn’t someone make an editor for the usage log to make it so that unwanted logs can be erased?
19 bushing // May 1, 2010 at 6:40 pm
First off — it’s not the “nandloader” that writes to the channel usage log, it’s a combination of the System Menu itself and then each title. See http://wiibrew.org/wiki//title/00000001/00000002/data/play_rec.dat
That being said, it’s all irrelevant. It’s easily deleted (“format system memory”) and there’s no sign that Nintendo looks at it at all.
20 marcusw.myopenid.com/ // May 2, 2010 at 11:19 am
Here’s hoping that bushing is currently working as a security consultant…he really knows what he’s doing and has been handling this entire thing very skillfully.
Oh, and bushing, if we don’t update our Wiis, we’ll lose the ability to use some service or other (at least this is how it’s been in the past). Can you tell us what form your solution will take and what its eventual aim and effect on Nintendo will be?
21 panzeroceania // May 2, 2010 at 9:54 pm
is it also possible that some things SHOULD be there, and if they are deleted it sends up a red flag just as much as something that is there that shouldn’t?
22 bushing // May 3, 2010 at 3:58 am
@marcusw: Thanks for the kind words. I specifically *don’t* want to get into what we have planned, because A) it will depend on exactly what further steps Nintendo takes — we’ll pick whatever solution will be most appropriate and finish coding it up — and B) I don’t want to give them any more ideas 🙂
As far as loss of ability — yes, the only reason that anyone ever updates is because you constantly get nagged to do so, and often the Shopping Channel breaks without it. I know. Whatever solution we come up with will address that; you’ll end up with a fully-updated system with the nasty parts disabled in some way.
23 bushing // May 3, 2010 at 4:01 am
@panzerooceania: Unless you’re talking about something like comex’s formatter (which completely erases the NAND filesystem and starts from scratch), that’s not really something we need to worry about. Generally, you’d be deleting modified versions of IOS and things that don’t belong on a normal system. If you were to accidentally delete too much — assuming your Wii still booted, if you went and did an online Wii System Update through the System Menu, it would install anything that was missing.
24 Wack0 // May 5, 2010 at 12:02 pm
Hmm.
If someone sent a wii in with some softmod like darkcorp installed, and the person running the check disk accidentally hit ‘yes, delete’.. would it remove all fakesigned IOSes ? =
25 Galaxy // May 7, 2010 at 12:36 am
@marcusw: there are also ways of updating and managing your own titles so that you don’t get cut out of the loop. One such prime example would be NUSDownloader > http://wiibrew.org/wiki/NUS_Downloader. You can use that to manually manage your titles and allow you to choose what and when to update should you wish to install a new menu without getting a volley of IOS updates in the process. Hope this helps others as well because you do NOT have to update and get the full platter treatment from Nintendo, losing fakesign capable IOSes etc.
26 OuahOuah // May 13, 2010 at 3:07 pm
So… if I send a Wii (fully brick after some “4.2 update” with “sciifii” tool) to Nintendo, will it be “not repaired” ?
Bootmii was in IOS and no preloader.
Brick happened during the 4.2 update through homebrew tool.
Only cIOS was installed (no *Corp and no preloader)…
27 Metalclay // May 26, 2010 at 12:35 pm
Bushing, not sure if you’re reading these posts, but:
http://gbatemp.net/t229326-full-brick-sent-to-nintendo?pid=2864044&st=0&#entry2864044
Not sure how to dump the NAND since I can’t get anything to load up, but if you’d like my wii, I’ll send it out.
28 NotAWiiHacker // Jun 3, 2010 at 7:11 pm
Okay, I know this isnt a current topic, but Ive read my Wii maual a few times over out of pure bordem…but What I found out is that purchased content moved to an SD card can not be played on a diffrent Wii UNLESS that wii has already purchased the content, so if you can find the Area where it Kepps a record of all the stuff instaled (channels) then you can try to find a way to wipe it.
You must log in to post a comment.